The Need for Open-Source Identity Management
By Sai Doppalapudi
June 1, 2022
Open-source Identity and Access Management systems are vital tools for guaranteeing cybersecurity in organizations. Secure credentials and user verification are essential to deflect and prevent most data breaches.
Identity and Access Management, or IAM, is the digital perimeter of today’s business; robust authentication protocols can help keep digital content safe.
What is IAM?
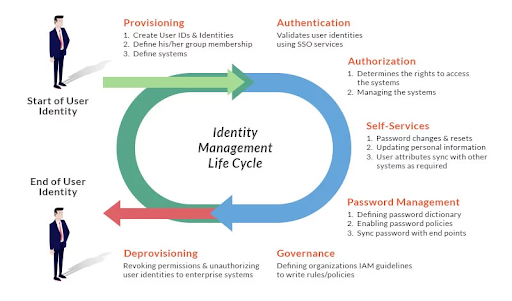
IAM is a security framework for enterprise web applications, APIs, user life-cycle management, and enterprise application access provided to external users and partners.
For IAM-integrated enterprise applications, IAM systems can regulate user or role-based access and provide a single sign-on login process for streamlined user authentication. IAM systems can also check user access requests and allow or deny authorization to enterprise-wide protected web and app resources.
All of these aspects of IAM help to regulate user hierarchy and heighten security within integrated applications.
To increase security further, IAM systems can be created as open-source. The term “open-source” refers to publicly available software. Since anybody can see and evaluate open-source code, such tools and solutions can be considered more accountable and informationally secure.
Advantages of Open-Source IAM
In comparison to closed-source or commercial software, open-source software has the following advantages:
Customization
Users and developers in open source communities typically come from various industries and backgrounds. Open-source software architectures are usually constructed to meet the demands and ideas of vast, diverse communities, allowing projects to adapt to changing requirements and/or roadblocks.
Furthermore, the IAM user experience should be adjustable to the needs of each developer, providing a differentiated digital experience from competitors; open-source IAM makes this possible by allowing extensions and modifications.
Low Cost
The return on investment of a project is directly impacted by incurring costs. The initial price of open source IAM is substantially lower than the retail license cost. Consulting services may be necessary to kick-start the project during its inception.
For an open-source IAM alternative, this is the only one-time non-recurring expense. After the project goes live, the only continuing costs are support and maintenance services, which are often less expensive than commercial choices.
Innovation and Flexibility
Organizations could speed up and reduce the cost of failure by fueling innovation cycles. Since there is no upfront investment expense, teams may quickly switch to another open-source IAM if the first or second IAM system fails to deliver promising results during its review period.
Freedom
Open-source software is entirely free to use, modify, and share.
Without waiting for a license, programs can be instantly utilized in evaluations or concepts. There is no need to go through a seller or fill out any forms to begin a project. The open-source licensing approach permits the software to be incorporated within a proprietary system and contribute value without any legal ramifications.
Quick Set-Up
One of the most basic requirements of businesses is a short time to market for their products or services. As a result, cloud-based solutions outperform on-premises alternatives when seeking quick setup.
Cloud-based IAM products such as Okta, Adaptive, CyberArk, and others perform brilliantly — These products can be used to launch a business’ IAM systems in minutes. It is, however, subject to each businesses’ requirements and personal goals. Other firms may prefer to focus on market growth before income growth.
Open-source tools like humanID are ideal for these types of businesses.
Why humanID as an Open-Source IAM Option?
Privacy
When it comes to privacy, humanID works best.
User Personally Identifiable Information (PII) is never stored; any user hash and hierarchy information that is stored is saved on the cloud.
humanID lets you know exactly what user data is needed and where user data is stored. With the help of this, your company can comply with privacy legislation such as GDPR, CCPA, and more.
User Experience
We’re all trying to wow our customers; therefore, improving the user experience is critical. With humanID, you can be authentic like a consumer-first company without any disruption in terms of branding and messaging.
Security is an important consideration when it comes to startups. You can’t just state that you’re more concerned with features than security. It is challenging to regain a customer’s confidence after it is lost. As a result, if you want to develop your firm, you must prioritize security.
Open source has become a game-changer for enabling UX-friendly security innovation, and humanID is a prime example.
Cybersecurity
Understandably, all organizations, large and small, are concerned about cybersecurity. Threats, cybercrime, and cyberattacks are all blocked with humanID authentication. With these robust adaptive authentication solutions, you can stop hackers.
Like proprietary and commercial IAMs, open-source IAM solutions are already gaining traction with businesses. Open-source IAMs offer unique value propositions due to their openness, usability, extendability, and low cost. Therefore, companies should consider them for their application’s user management use cases.


