What Login Should I Use For My New
Social Media App?
By Derek Quach
October 5, 2022
Social media has exploded in popularity. From 2010 to 2021, social media platforms have tripled their total user base. As of August 2022, there exist 4.7 billion social media users compared to the 970 million in 2010. An online social network, or social media, is a “website or application that enables users to create and share content” (via Oxford Languages). This shared content extends beyond just family and friends and allows sharing and networking with strangers. Platforms such as Facebook, Instagram, and Twitter allow users to access this content. Although these platforms, in terms of monetary value are free, the cost of entry is not. The price of admission is a login.
Regardless of their social standing or wealth, every user pays for their choice of social media. And since each instance of social media use begins with the user login it may be difficult to decide which one to use. But first, let’s explore what elements a good login should have.
Protection
First and foremost, logins should be safe. Generally, most users are granted account access through password-based authentication. However, this type of authentication is becoming increasingly unsafe. Methods of authentication such as biometric authentication, MFA, and SSO have provided users protection from password-related attacks.
In the first case, biometric authentication is used by smartphones such as the iPhone or Samsung Galaxy. This requires facial, or fingerprint recognition for users to access their phones. Though this method is safe and convenient, it isn’t necessarily viable on desktops and requires the storage of biometric data. This type of authentication is also not feasible as breaches would put biometric data at risk. Additionally, users may not like the idea of submitting their biometrics to a social media app. Smartphones typically store this data locally, or in a compartmentalized chip in a device mitigating the risk of stolen biometrics. This idea of compartmentalization is important.

On the other hand, MFA, or multi-factor authentication, requires further authentication through a phone number, email, or secondary authentication provider. Through the aforementioned communication methods or providers, a code (typically numerical) is sent to you. With this code, you can verify your identity by submitting it to the original website. It’s a process that may seem excessive, but MFA is quite effective. As a testament to this, it’s employed by companies such as Amazon, Microsoft, and the U.S. Department of Defense. Nevertheless, MFA doesn’t eliminate the problem of reused passwords. Convenience, as we’ll soon learn, is as important to security when implementing a login.
Convenience
If you’re lucky, your choice of social media will remember your information– rendering the login page absent. Without this feature, you and users alike are required to re-enter their passwords. Of course, this is inconvenient and encourages users to create recycled passwords. Relatedly, account access through stolen or weak credentials accounts for 81% of hacking-related breaches. This figure suggests that returning users, and potential clients, naturally prefer convenience while using their most visited websites.
Although, it is not only users that prefer convenience. Software developers are notorious for “us[ing] existing code for […] software”, otherwise known as code reuse. This provides great efficiency and has helped developers build websites and apps like Google, Instagram, and Twitter. In the same vein, they develop each of these websites’ logins which begins with password-based authentication. But, based on the correlation between weak passwords and hacking-related breaches, password-based authentication is becoming inconvenient.
Chances are you will have to implement password-based authentication. However, you can save the user time and mental effort by reducing the number of passwords they have to remember. By implementing single sign-on, users are able to securely and conveniently access their accounts.
Both biometric authentication and MFA have their advantages and disadvantages, SSO or single sign-on provides a great middle-ground solution to safe and convenient logins. While it sounds unsafe to use one set of credentials, that’s because it generally is. At least if it’s implemented poorly. SSO is highly dependent on the identity provider.
Single Sign-on
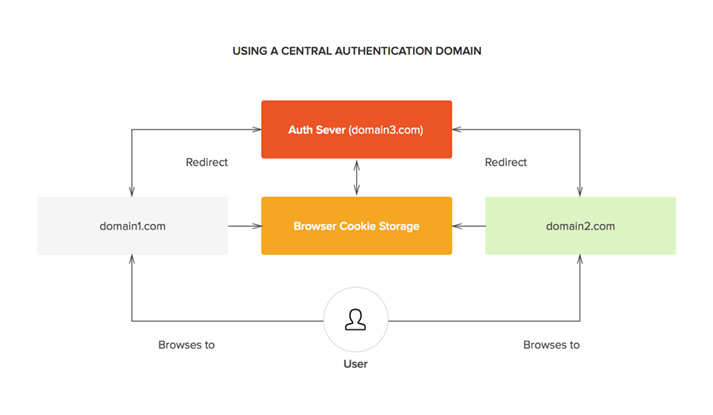
SSO is built upon a foundation of trust between multiple parties, SSO works as the user accesses and logs into a website or application (otherwise known as the service provider). The service provider then sends a token, or “collection of data or information,” like an email, to the identity provider. If the identity provider finds that the user doesn’t have a previous login, it will ask them to create a new set of credentials– typically with a username and password, or a one-time password. If the user already had a set of valid credentials, or if they’d just created one, the identity provider can then authenticate the user’s credentials.
With the foundation of trust in mind, the identity provider can send a token back to the service provider. If need be, the service provider can then validate the token it received. Afterward, access to the service provider is then granted to the user. Impressively, all of this is done with a click of an SSO button.
It sounds complex, but a well-implemented SSO login is quite safe. And by introducing SSO as a primary or secondary method of login, user logins are compartmentalized through a trusted party. Compartmented logins, much like how biometric data is compartmented, reduce risk since an SSO button can just be removed. But hopefully, you won’t need to.
Conclusion
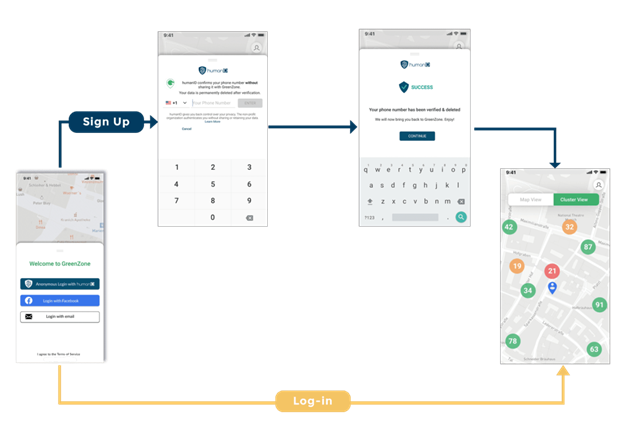
In summary, both secure and convenient logins are aspects to consider when implementing a login. If implemented well, SSO provides a great middle-ground for a reliable and easy method of login. Providers such as humanID would provide convenience as it places its method of authentication right into the user’s hand– their cellphone. humanID also provides user security as it never stores data beyond the login, therefore mitigating the chance of stolen data. It seems humanID provides the perfect solution for safety and convenience, but as importantly, it provides peace of mind.
P.S. Social Media Management is Important!
If you’d like to bolster your knowledge of social media management, consider devCount’s recommendations. devCount’s ‘15+ Best Social Media Management Courses Online in 2022‘ offers concise insight into where you can find these modern online resources. Implementing safe, convenient logins and better managing your social media platform will proffer your users an improved experience.



