Malicious Life and humanID: A Better Internet
By Evan Walters-Zucco
July 12, 2021
The internet is plagued by data collection, data leaks, bots, hacking, and disinformation. Large corporations, such as Google, Facebook, Apple, Amazon, and Microsoft, collect and monetize the data they gather from users. This is because data is highly versatile and profitable, making it the most valuable asset in the world. As a result, data collection and monetization have turned these tech companies into billion and trillion-dollar monsters. These same corporations also benefit from bots and misinformation. Consequently, these already thriving corporations have no reason to create a better internet that secures users’ privacy and safety. Unfortunately, politicians also lack the incentive to crack down on these companies as it would economically impair the United States. Apple, Amazon, Google, Microsoft, and Facebook generated a combined $899.2B in 2019, making it the 18th largest country by GDP. This rate of production is only accelerating as the tandem has generated $322B in Q1 of 2021 already.
humanID was founded with a mission to solve these issues. At humanID, we believe in a bot-free internet that is free from misinformation. To accomplish this, we provide privacy and online anonymity in tandem with accountability. Cybereason, likewise, strives to make the internet a safer, better place. Their technology stops sophisticated attacks before they ravage networks. To spread awareness about the implications and commonality of cyberattacks, Cybereason produces the podcast Malicious Life. Malicious Life is hosted by Ran Levi, who interviews hackers and industry experts, diving deep into the hacking culture of the 1970s and 80s, as well as today’s issues. There are now 123 episodes and counting, containing highly informative and entertaining information on cybercrime and cybersecurity. Levi has also explored cyberwarfare in multiple episodes, making it universally topical. humanID and Malicious life are a constant reminder that cybersecurity is a necessity not only for business but for individuals as well.
Cyber Warfare

Technology has fundamentally changed the world. Unfortunately, people, organizations, and even countries utilize malevolent ways to exploit technological advancements to their benefit, regardless of the damage. This includes utilizing technologies such as phishing, malware, distributed denial-of-service (DDoS) attacks into warfare, expanding the very definition of warfare itself. While warfare often connotes lethal force, cyberwarfare has added a new dimension of non-lethal methodologies. In the Malicious Life podcast, Levi talks about China’s unrestricted warfare in episodes 113, 115, and 119 in Season 3. These episodes give the listener a deep understanding of the tactics China has been deploying that often go undetected.
In the first of the three episodes, Levi interviews Bill Hagestad, who in 2015 sat next to Wang Xiangsui, coauthor of Unrestricted Warfare. Unrestricted Warfare is a notable military strategy book due to its successful predictions of the 9/11 attacks and cyberspace as a medium for war. Liang and Xiangsui successfully foresaw the use of hackers in warfare by envisioning the use of computers compromising armies and nations remotely. Being that the book was published in 1999, their predictions were bold but ultimately correct.
The Dangers of Bots and Misinformation
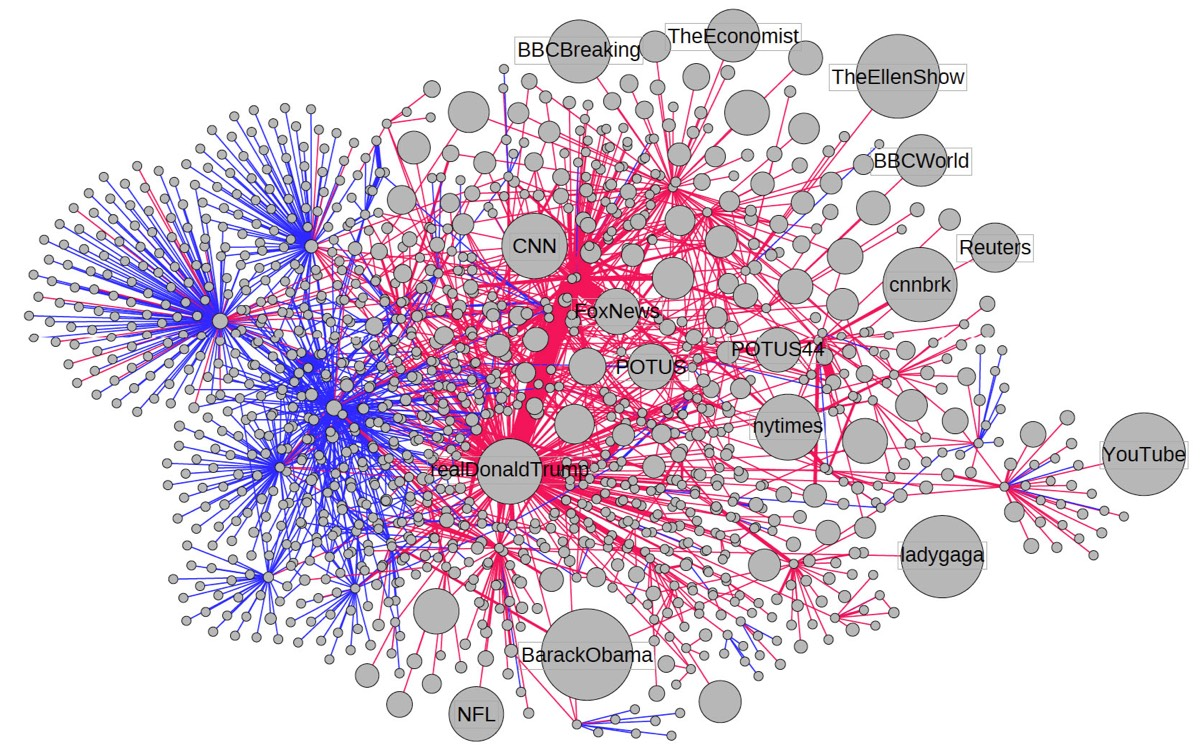
Recently, the use of cyberspace as a medium for war has become increasingly relevant. While it might not be glaringly obvious at first, the presence of bots and the rise of misinformation are the actualization of Xiangsui and Liang’s writing. Bots are often regarded as simply annoying and generally harmless. However, bots are far from harmless while still annoying. On Twitter, there are an estimated 48 million bot accounts, making up about 15% of all users. On Instagram, there are an estimated 95 million bot accounts, around 10% of all users. With significant numbers and percentages, bots can make their presence felt on social media. On Twitter, an estimated 20% of global trends are created from scratch by bot accounts. Most of these trends involve misinformation, gambling promotions, and hate speech. This is increasingly worrying as social media is synonymous with daily life as roughly 50% of the global population uses social media. As a result, misinformation created and spread by bots is an existential threat.
Due to a complete failure to regulate tech monopolies, Facebook, Twitter, and Google have turned into monopolies that are more powerful than other countries. These three companies form an oligarchy in the advertisement space due to the vast user data they possess. However, this power is often abused and misused to churn a profit. Facebook’s wrongdoings are not minuscule anymore, and their effects are felt globally. In Myanmar, Facebook was accused of censoring activists and journalists reporting on the ethnic cleansing of the Rohingya minority. Despite Facebook admitting to being used to incite violence in Myanmar, they have failed to resolve the issue in Myanmar and to stop similar instances. Furthermore, Facebook is still promoting content urging violence against protestors in Myanmar. Facebook has also been cited to increase attacks on refugees by 50% in Germany and acknowledged that they knew about the threat of January 6th but failed to take any actions. The company has taken a clear stance, they plan to let extremist groups plot and eventually act violently as there have been little to no repercussions against them.
Twitter is also a large proponent of misinformation and bots. On Twitter, misinformation is 70% more likely to get retweeted than accurate news. Misinformation also consistently reaches a larger audience while simultaneously tunneling deeper into social networks than accurate news does. Twitter, like Facebook, also received a lot of criticism during 2016, seemingly unable to please anyone. They also received further backlash from a report that a partner of theirs, Dataminr, was using Twitter to profile and surveil communities of color during the Black Lives Matter protests.
While Facebook and Twitter often receive most of the criticism for their role in spreading misinformation due to being inherently more political, Google also presents issues. Google, like Twitter and Facebook, profits from misinformation. Google attempted to launch a censored search engine named Dragonfly in China but ultimately abandoned the idea due to public backlash after The Intercept leaked reports. They have also been linked to spy tech that the Chinese government utilizes to spy on its citizens. This is not the only privacy concern Google has faced; in 2019 the Federal Trade Commission fined them $170M for violating the Children’s Online Privacy Protection Act (COPPA). Currently, Youtube is plagued with bots impersonating Youtubers to scam viewers with nothing being done to change this.
While Facebook, Twitter, and Google are distinctly unique, they share a commonality: their dangerous algorithms. In order to continue generating profits and revenue to please shareholders, they utilize their highly addicting and exploitative algorithms. These are used in tandem with the bots and misinformation, often encapsulating users in an echo chamber that would be impossible to replicate; this is very calculated on their behalf. By continuously gathering user data, these algorithms can find content that will have the user glued to their device for hours, consistently generating revenue for big tech companies.
How to Prevent Cyber Warfare

As mentioned above, bots and misinformation are existential threats. Misinformation, when undealt with, can create conflict and even result in death. Bots have been an effective method to spread misinformation at a rapid speed while simultaneously making it look legitimate due to high interaction on social media. humanID offers a solution to these problems and the Malicious Life podcast provides informative and entertaining content to keep you aware.
humanID is a one-click, anonymous login solution that secures the user’s privacy and anonymity while simultaneously preventing spam and bot misinformation. This is done by our unique approach of utilizing the user’s SIM card to create a unique ID. Each user is also assigned a nonreversible, hashed identifier. The phone number is used as the irreversible, hashed identifier, allowing for verification of the user’s credentials from numerous applications while preventing the creation of spam accounts. In addition, we further ensure privacy and security by deleting the user’s data from databases upon authentication. There are also two levels of hashing to ensure privacy and security. First, the user’s phone number is hashed and then instantly deleted. After the first hash, the salted hash is then stored as the username for the specific applications login. By having distinct hashes for each application, we can safeguard their information while allowing access to multiple platforms. humanID not only saves time by eliminating usernames and passwords but also provides extra security with privacy.
The Malicious Life podcast tells the history of cybersecurity. Although cyber history is generally younger, it is still widely unknown. Levi and Malicious Life effectively combat the general lack of knowledge of cybersecurity history by providing and creating entertaining episodes with topical guests. These guests range from hackers to cybersecurity experts and even journalists and politicians. By gaining an understanding of the history of cybersecurity, you will be able to more effectively understand the risks of the internet.
Ultimately, tech companies have shown no interest in combating bots or disinformation as they profit off of it. humanID is a solution to that problem. However, in order to keep your privacy safe and to avoid falling victim to cyberattacks and misinformation, keeping yourself educated is a must. The best way to do so is to listen to the Malicious Life podcast. Malicious Life already has over 120 episodes of entertaining and educational content on multiple platforms including Apple Podcasts, Spotify, Stitcher, and Malicious Life site. By listening to the podcast, you too will be able to identify cyber threats easier and become more tech-savvy.


