How to (Not) Get Hundreds of Burner Numbers
By Brennan Whitfield
January 7, 2022
How disposable is a phone number? Imagine you are an employee assigned to direct a spam attack against a competitor company’s website. Your initiative is to overwhelm the website’s servers to drive user activity to your company’s site instead. To carry this out, you must create multiple accounts to produce as much activity as possible, and the site requires a phone number to make said accounts. “Simple”, you believe; you plan to use burner numbers for each account. Though, is it really as easy as it seems to use burner phone numbers in large capacities?
Why Use a Burner?
A “burner” refers to a prepaid phone communication line which is cheap and not intended for long-term use, with the end goal being that both the line and data are disposed of (“burned”). This type of phone line originally described a throwaway physical device, usually a cellular phone, but more commonly now refers to solely a throwaway phone number. These aspects of having a quick and inexpensive method of communication are what has made burners so popular.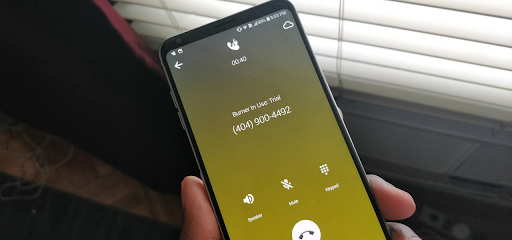
Standard phone numbers are easily traceable back to its owner, giving it a record of being a reliable identifier when asking online users for human verification — one phone number equals one user. Though, this method of authentication has been questioned with the prevalence of users creating accounts with burner numbers instead. Popular phone applications such as WhatsApp, Tinder, and TikTok all require a phone number to create an account, but there is nothing stopping users from inputting burner numbers. In theory, this can seemingly spell trouble in the scenario mentioned before if attackers were to carry out a distributed denial-of-service (DDoS) attack or similar on a digital platform. In practice however, obtaining a mass amount of burner numbers is a more difficult task than it appears to be.
The Impracticalities of Using Hundreds of Burners
Costs
In a study conducted by Red Wolf Security, the organization states that to simulate a realistic DDoS situation at least 400 different IP addresses are needed to properly disrupt a network. Burner, one of the best known phone applications for providing burner numbers, offers one number at a monthly base price of $4.99. Taking these two variables into account arises the issue of expenses when acquiring burners for spamming purposes.
Assuming the average cost of a burner number is around the price of $4.99, and one burner is delegated to one IP address, this would equate to almost $2,000 for an attack to be coordinated and conducted in the time window of one month. Coordinating an effective bare-minimum spam attack equates to a costly endeavor, and only for a limited timed window.
Time-Consumption
Similar to expenses, managing multiple burner accounts and numbers becomes a large consumption of time. As reported by Statista, the average time for a user to install an app and sequentially register afterwards was recorded at around four minutes for brand apps, and around five minutes for marketplace apps.
With consideration of the amount of required IP addresses in the scenario by Red Wolf Security, assigning four to five minutes of time for creating burners manually for each IP would equate to a total of 1,600 to 2,000 minutes. In addition, email addresses are frequently required to register for burners. Since creating an email and creating a burner account itself would be needed for each IP, the total time above in reality would be doubled to 3,200 to 4,000 minutes (~53 to 67 hours).
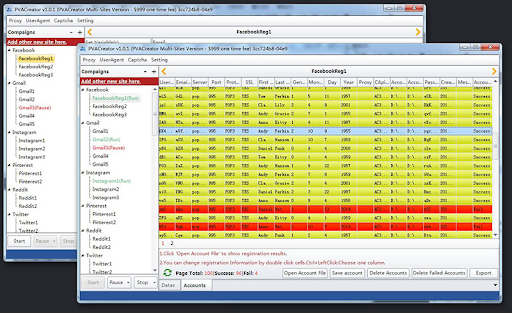
To bypass this roadblock, attackers have attempted to use the assistance of bulk account creators to create multiple accounts at once, though this type of software is not always reliable either. PVA Creator in particular, one of the top search engines results for bulk account creators, has been cited with numerous mixed reviews. Claims of experience have been riddled with scamming, malware, and recurrent crashing from using the service, displaying a difficulty in finding reliable software to limit time in mass burner registration.
Recycled Numbers
Today, there are not enough phone numbers to account for every individual on the globe. To keep up with the demand of phone usage, around 100,000 phone numbers are reassigned each day as noted by the FCC. This recycling of numbers is applicable for burners as well.
Research conducted by Wonder found that about 45% of cell phone users change their phone number every two years or longer. Looking at burner numbers in conjunction, it is unlikely they will stay to one device for so long considering the nature of its use. As such, burner numbers appear to be more likely to have already been registered to an online account by a different user, versus a non-burner number. In an ideal scenario where someone has acquired both the expenses and time for enough burners to conduct an attack from Red Wolf Security’s scenario, the burner numbers gathered may not all even be valid for use in the first attempt.
How humanID Discourages DDoS and Burner Number Use
Seeing above, phone number authentication upon login can make it increasingly difficult for DDoS and similar attacks to be carried out. Comparing with email authentication, creating email addresses are free of charge and not generally consistent with the one email equaling one human rule, making a site with this authentication more vulnerable to mass bot attacks. Using phone authentication ensures a more precise user verification process and supports a more bot-free environment.One such service that offers reliable phone number authentication and protection for platforms would be humanID. humanID is a single sign-on (SSO) solution which works to prevent spam attacks and traffic flooding by bots. While humanID is implemented onto a platform, a user creating an account will be asked for their phone number to prove human identity. What sets humanID apart from other SSO solutions however is its ability for anonymous browsing.
Following phone authentication through humanID, the user’s number is immediately hashed then deleted, allowing them to navigate the platform in complete anonymity. With humanID, the technology aims to foster an environment which encourages both user privacy and user voices uncluttered by bot traffic.


